Multiparty Computation Unlocks Privacy for DeSci
Privacy series - MPC Spotlight
Intro
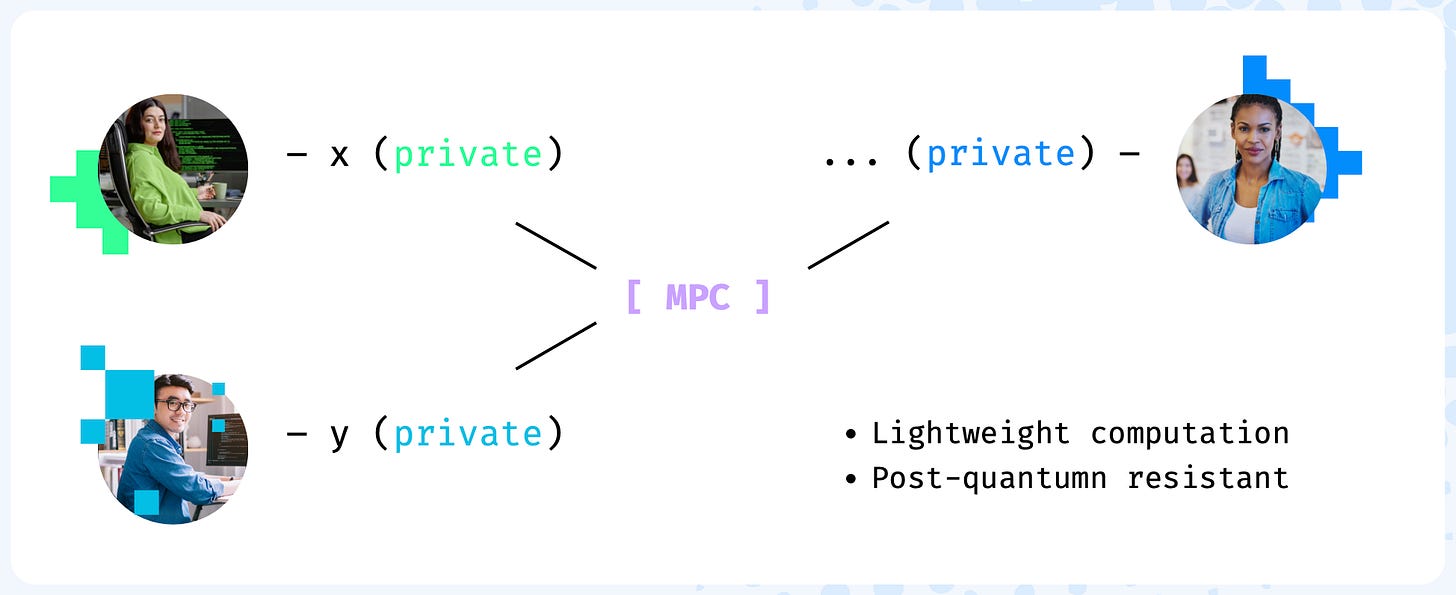
What if you could jointly analyze data without ever sharing it? This would solve multiple problems for Decentralized Science (DeSci) including data privacy concerns, restrictive data sharing policies, and coordination issues that have left many projects struggling to scale. Today we kick off the first article in a series of three talking about privacy preserving methods for DeSci. Today we will be talking about Multiparty Computation (MPC) which is what are partners at OpenMatter Network use to secure data for scientists. MPC is a form of cryptography that lets multiple distrusting parties analyze data together without ever sharing it. We refer to this as collaborative computing. Collaborative computing has been around since the 1980s but only in the last five years or so has it become scalable enough for Blockchain. Today we are going to focus on how MPC unlocks new privacy for DeSci and why now is the perfect time for projects to start exploring MPC.
How it works
Imagine three researchers are working on highly sensitive patient data and want to collaborate together to combine their data for deeper insights. Unfortunately the project requirements are restricted due to HIPAA compliance and patient data cannot be leaked under any circumstances. So what do you do? How do you enable trustless collaboration on sensitive data? Enter MPC - the powerhouse of cryptography for collaborative computing.
Let’s break it down:
Each party provides their data using a secret sharing process
MPC nodes analyze the secret shares
Data is analyzed in secret and returned back to the users
Privacy preserved and raw data is never shared with any other party
MPC Setting
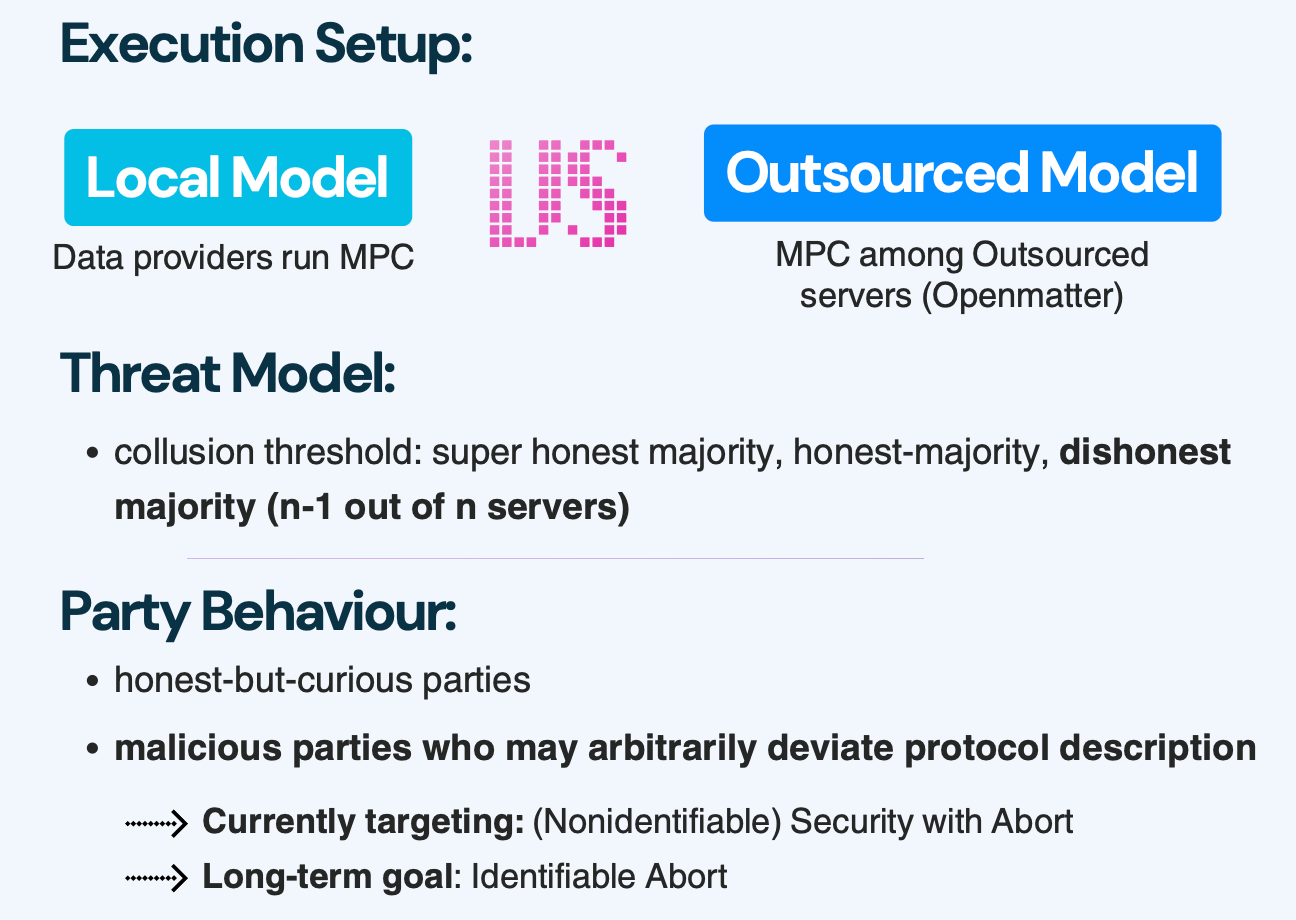
Not all MPC protocols are created equal. In fact, many MPC protocols today are using weak security requirements that are not post-quantum secure. This means your data is at risk of leakage in the event of a quantum attack. This is not the case for OpenMatter Network which is our MPC partner. Let’s break down the security assumptions of the OpenMatter protocol.
Execution setup: Scientists provide secret data to a decentralized compute network. This ensures the MPC scales.
Threat Model: OpenMatter is secure in the dishonest majority setting. This means that even if 2/3 of the parties provide malicious data or try to cheat on the protocol security and integrity can still be guaranteed.
Party Behavior: OpenMatter is secure against active malicious parties. In this model it is assumed a malicious actor will try to cheat and provide bad data or try to learn what they can about the other parties data. In the event this happens the protocol will abort and the MPC will fail. In the near future, OpenMatter will implement identifiable abort and cheaters will be slashed.
This model presents the strongest security assumptions MPC currently has to offer and is what is being built at OpenMatter.
Conclusion
In this article we covered the basics of MPC and how OpenMatter is building the state of the art with the highest security guarantees. Next in the series we will be diving into more specifics about MPC protocol design and the efficiency tradeoffs.